|
Messageware Z-Day Guard for Microsoft Exchange Server |
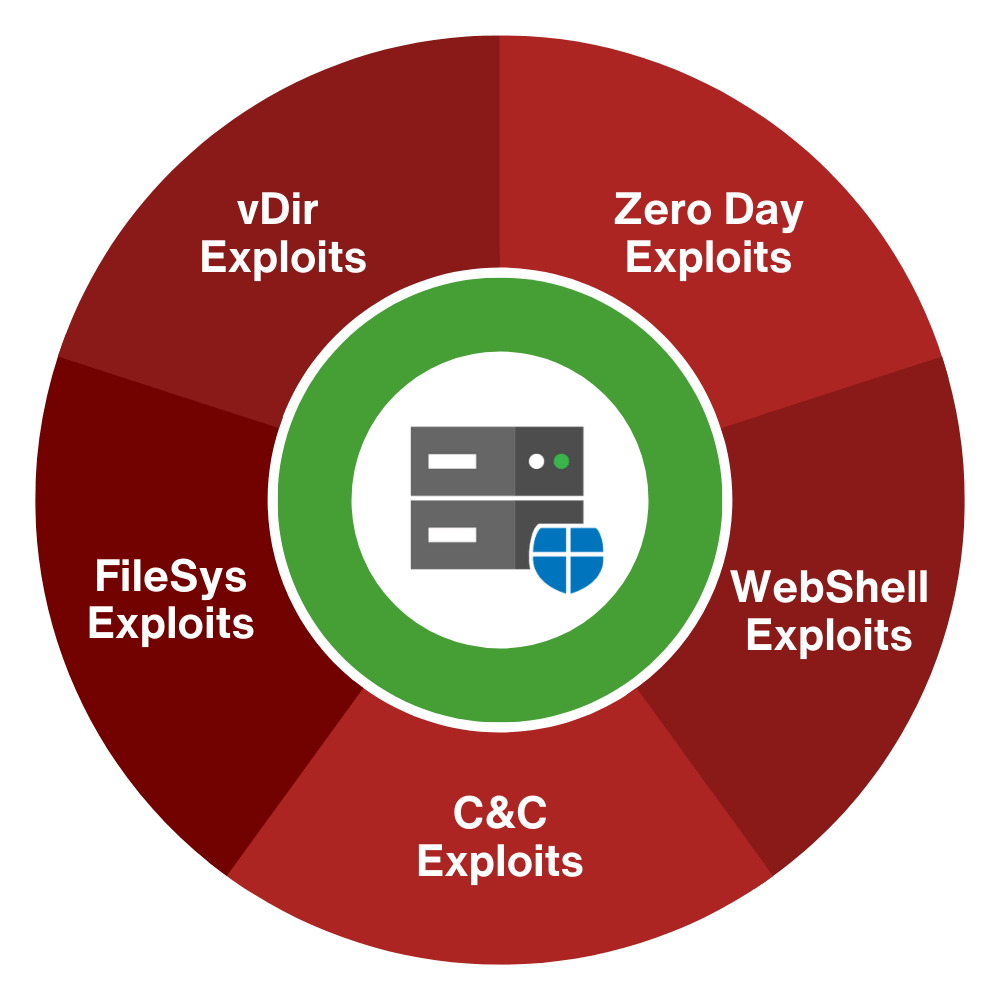
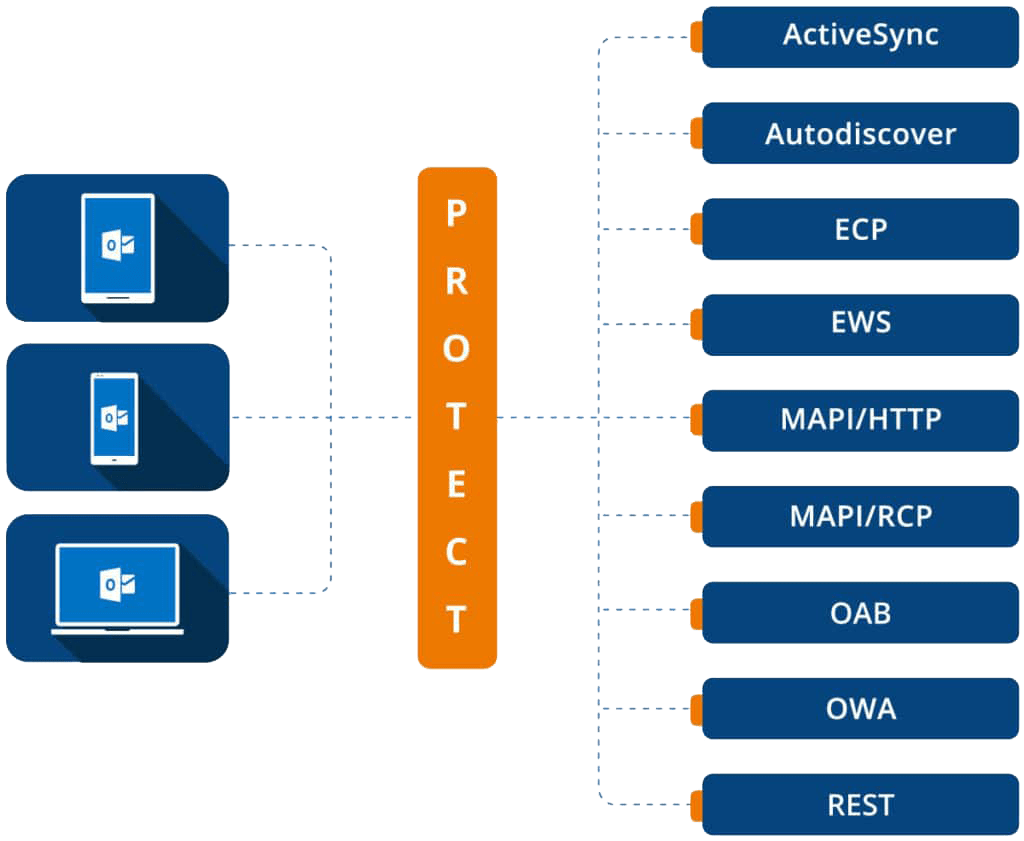
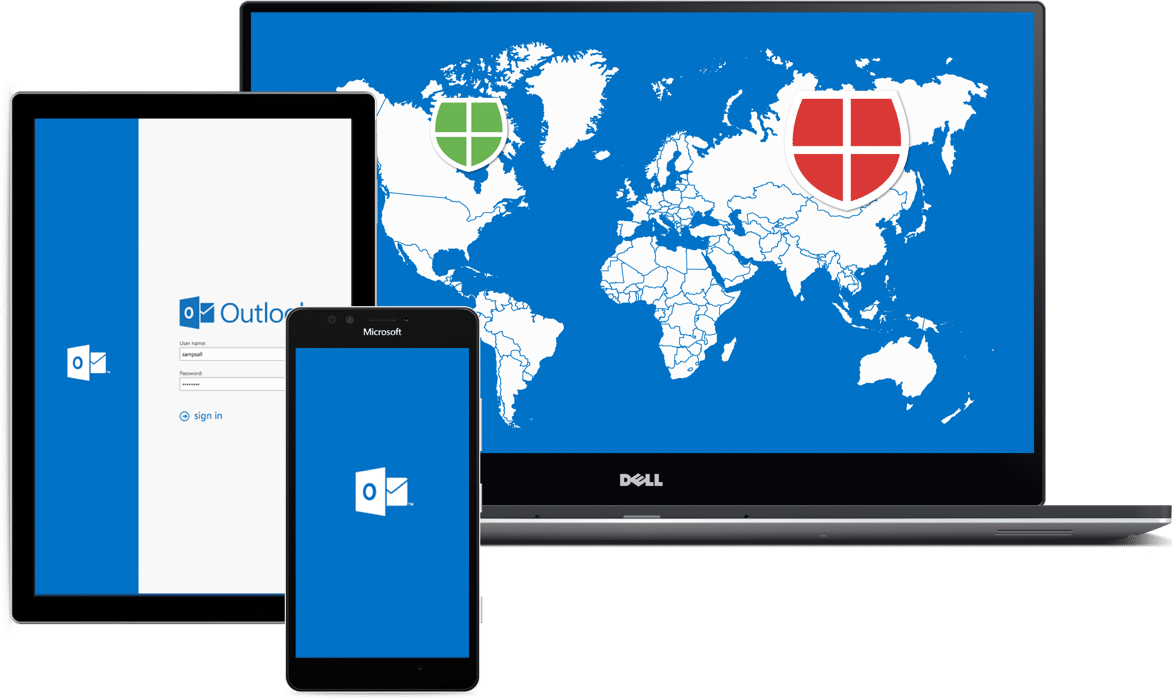
Next generation threat hunting that cannot be turned off by malicious software. Monitor your Microsoft Exchange servers against zero-day attacks, with detection, alerting, and response (MDR/MDAR) to server penetrations.
Messageware for Exchange Server Security
Protect corporate data with strong Messageware Attachment, Logon and Session security. Monitor, collect and analyze security intelligence data. Enforce corporate security policies. Built for Microsoft Exchange Servers.

OWA Enhanced for Firstline Workers
OWA Desktop and ActiveSend provide a fast and seamless Outlook Web experience on Microsoft Windows workstations. These two products make Outlook Web more like Outlook and enable OWA to be the Windows default mail client.
“Organizations can leverage all the benefits of cloud-based email, without the transitional headaches. It’s customizable, easy to deploy, flexible–and best of all it saves real money.”
Office 365: Apps and Add-ins
Windows Desktop Control and Integration with Office Applications. All Outlook platforms and mobile devices. Email Forms, Email Templates, Mail Notifications, Calendar Reminders, and more. On-premises Applications and Add-ins that bring improved convenience, productivity and functionality to the Outlook, Outlook Web and Outlook Mobile user.

Consulting and Development Services
Develop the functionality you need to maximize your investment in Office 365 and Microsoft Exchange Server. Design and build with the new “zero-footprint” Office Add-ins that seamlessly extend Outlook, Outlook Web and Outlook Mobile clients.